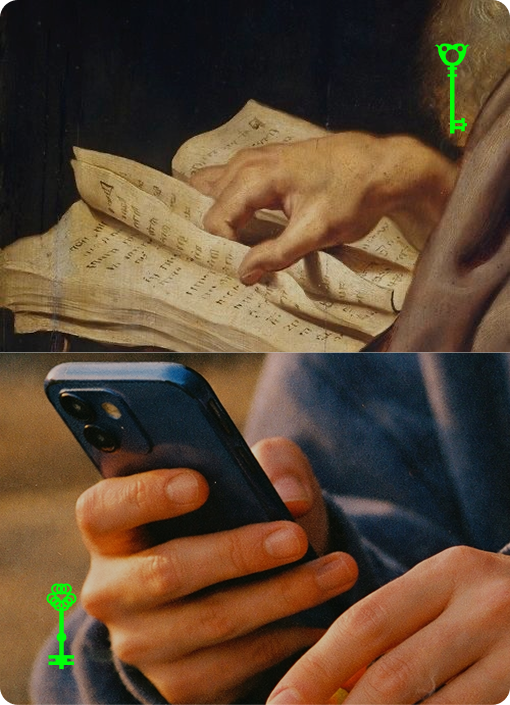
The most meaningful creative and social coordination on the internet happens in private groups, closed communities, invite-only spaces. The topology is private-first.
Every existing system collapses proof and content into the same surface. If you can't access the content, you can't verify anything about it. DFOS separates them.
The world of proofs is public — signed chains that anyone can verify. The world of content exists in dark forests — member-governed spaces, visible only to participants. The protocol defines the proof world. It sees hashes, never documents.
Identity is a chain of cryptographic operations you control.
Your did:dfos identifier derives from
your genesis — self-certifying. Forks are valid. Convergence is deterministic.
No consensus needed.
Verification is a pure function. Public key + signed chain = valid or invalid. Any Ed25519 library, any language. The chain carries everything needed. A proof exported today is verifiable by code that doesn't exist yet.
Web relays independently verify every operation on ingestion. No trust between relays. No hierarchy. Topology is emergent. Three peering behaviors compose the network: gossip, read-through, and sync.
Same deterministic test vectors across all five implementations. The protocol specification is the single source of truth.
One binary. Keys in your OS keychain. Local-first by default. Full documentation.
curl -sSL https://protocol.dfos.com/install.sh | sh
Also available via
brew install metalabel/tap/dfos
and
docker pull ghcr.io/metalabel/dfos
# create your identity
dfos identity create --name myname
# publish your first post
echo '{"body":"gm"}' | dfos content create -
# see it
dfos content list
# run a relay
dfos servedid:dfos — self-certifying, transport-agnostic identifiers Content Model JSON Schema content types committed via content-addressed CIDs Credentials Delegated authorization, revocation, standing access, and attenuation Web Relay Verifying HTTP relay with gossip, read-through, and sync peering Sign In With DFOS Cryptographic identity verification for third-party applications